 This month’s Hobby Tech column is taken up with a trio of reviews covering the pretty darn impressive Mooltipass Mini hardware password manager, Automattic’s Blog in a Box distribution for the Raspberry Pi, and Mark Hardisty’s A Gremlin in the Works.
This month’s Hobby Tech column is taken up with a trio of reviews covering the pretty darn impressive Mooltipass Mini hardware password manager, Automattic’s Blog in a Box distribution for the Raspberry Pi, and Mark Hardisty’s A Gremlin in the Works.
Starting with the latter, A Gremlin in the Works is another fantastic coffee-table book from retro computing publisher Bitmap Books (the founder of which, Sam Dyer, I interviewed back in Custom PC Issue 136). Written by Mark Hardisty based on exhaustive interviews – and retaining the question-and-answer style of the transcripts, making for an accurate rendition of the subjects’ thoughts but a slightly tiresome read – the two-volume book chronicles the rise and fall of gaming pioneer Gremlin Graphics. As a massive fan of Gremlin’s output – to this day the intro music to Hero Quest brings joy to my heart, and I blame my sweet tooth on a Zool addiction – A Gremlin in the Works is a book I’d long been looking forward to reading, and I’m pleased to say it didn’t disappoint.
Blog in a Box, meanwhile, is an interesting beast. At its heart, it’s a single-purpose GNU/Linux distribution for the Raspberry Pi created by Automattic as a means of making it easier for people to run the WordPress blogging platform from the device. It’s not provided as a downloadable drive image, as with most distributions, though; instead, Automattic has written a cross-platform program which customises various settings – title, passwords, email accounts, things like that – and configures them so the Pi is ready to rock on first boot. It’s a neat idea, but one which still needs polish: I found the Linux version failed to run properly on my Ubuntu 16.04 desktop, and several features promised by the tool were disabled when the Pi actually started up. It’s a tool with promise, though, and I look forward to revisiting it should Automattic release an update.
Finally, the Mooltipass Mini. The brainchild of Mathieu Stephan, the Mooltipass Mini builds on its non-Mini predecessor to create a pocket-sized hardware password safe for all your accounts – or, at least, as many as will fit in 8Mb (1MB) of internal memory. The Mooltipass Mini is a tool for the adequately paranoid: passwords, though not usernames, are stored in the device’s internal memory under AES-256 encryption with the private key located on a removable smart card itself locked with a four-hexadecimal-character PIN. When a password is required, its entry can be found on the screen and the Mooltipass does its best impression of a USB keyboard by typing the account details in on your behalf – or, when the optional software is installed, filling in forms in browser windows automatically upon manual confirmation on the device itself.
Having long advocated for the use of password managers to promote high-quality password use and discourage password reuse, the Mooltipass Mini is a near-perfect companion. It addresses the majority of the problems with traditional password managers, like how to keep the encrypted database accessible while preventing its theft. While there are undeniable issues, such as the £61 (inc. VAT) retail price and the need to buy two so you have a backup to use if the primary one fails, it has become a part of my security arsenal – and one I feel comfortable using thanks to the project’s open-source nature for both the software and underlying hardware.
All this, and a whole mess of other things written by people who aren’t me, is available in the latest Custom PC Magazine from your nearest supermarket, newsagent, or electronically via Zinio and similar digital distribution services.


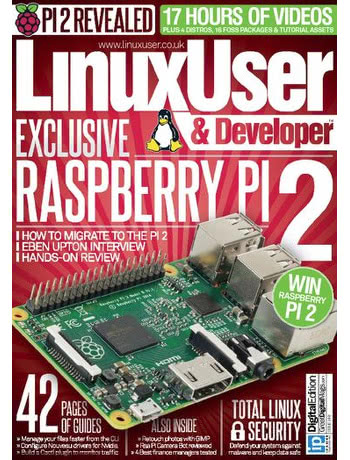 This month’s Linux User & Developer features my usual four pages of news from the world of openness alongside a review of some interesting software I’ve been playing with: Keybase.
This month’s Linux User & Developer features my usual four pages of news from the world of openness alongside a review of some interesting software I’ve been playing with: Keybase. For the hundred-and-first issue of Linux User & Developer, two reviews and a feature: a group test of backup software can be found at the bottom-left of the cover billed as “Keep your data safe the open source way,” while to the right can be found a LibreOffice review. Finally, a hardware review of the Hiddn Crypto Adapter, which is a truly impressive bit of kit, by the way.
For the hundred-and-first issue of Linux User & Developer, two reviews and a feature: a group test of backup software can be found at the bottom-left of the cover billed as “Keep your data safe the open source way,” while to the right can be found a LibreOffice review. Finally, a hardware review of the Hiddn Crypto Adapter, which is a truly impressive bit of kit, by the way.